Posts Tagged ‘SNMPv3’
Wireshark Tid-bit: De-crypt SNMPv3 in Wireshark
I recently found myself troubleshooting some SNMP connectivity between a particular set of devices and an NMS. Connectivity did not appear to be the problem as IP Connectivity was there and MIB walks were successful, however some interesting errors were still getting reported on the NMS. As I captured the packets to verify this connectivity, I said to myself ‘If only I can see what the NMS was asking for specifically and what device in question was replying back with’. This led me to check out the SNMP protocol settings in Wireshark, I mean Wireshark can de-crypt HTTPS traffic (with the private key) and wireless WPA traffic surely it can de-crypt SNMPv3. Behold it was true!! I was able to de-crypt SNMPv3 packets, and see what was really going on.
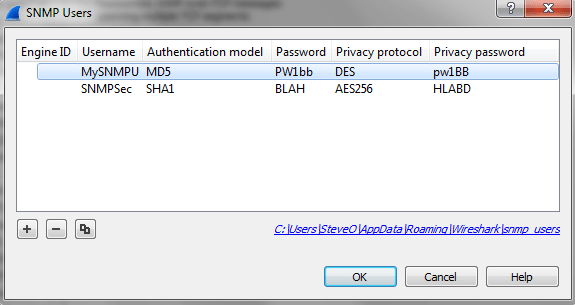
To add SNMPv3 information into Wireshark:
Access your Wireshark preferences: Edit -> Preferences -> Protocols -> SNMP
Where you see ‘Users table’ choose edit:
From here we can enter the SNMPv3 settings we need:
- Engine ID
- SNMP USer
- Authentication & Password – MD5 or SHA1
- Privacy & Password- DES, AES-128, AES-192, or AES-256
Once you enter the correct information and choose ‘ok‘ Wireshark will automatically de-crypt any relevant packets.
I feel like this is something I should have known about for a while now, but I supposed I don’t find myself troubleshooting SNMP connectivity too often. Figured I would get the word out there!
An overview of SNMP,
Simple Network Management Protocol (SNMP), it’s a protocol that has been around for a long time and exist across the board on networking devices, servers, firewalls, UPS, and just about any other device you can name that we use in the IT field. It’s a standard management protocol defined by IETF for managing devices.
Their have been a few different versions of SNMP over the years, starting with SNMPv1 however short comings were discovered with this implementation the most notable being its lack of security. Then came SNMPv2c which is backwards compatible with SNMPv1 however SNMPv2c offers more security than its predecessor however I feel security is still lacking in SNMPv2c. The newest implementation of SNMP, SNMPv3 offers both Authentication and Encryption providing SNMP with the level of security it deserves.
SNMP relies on 3 pieces a
- NMS– Network Management Station, this is the device that collects the SNMP information from the networking devices it is managing.
- Managed Device– This is the device that is being managed by the NMS.
- Agents– An agent is the application that runs the SNMP process and contains all the local management information on the managed device.
Now the NMS gathers its management information by sending request to the manged devices and the managed device responds with the desired information. The follow packet types are used with SNMP:
- GetRequest -Sent by the NMS to the managed devices asking for the managed device for information.
- SetRequest -Also sent by the NMS to the managed devices, asking the managed device to change its configuration or a value.
- GetNextRequest -Again sent by the NMS to the managed devices where the NMS is requesting additional information from a previous request.
- GetBulkRequest -Introduced in SNMPv2 as a replacement to the GetNextRequest.
- Response -Sent from the managed device to the NMS in response to a GetRequest, SetRequest, GetNextRequest, GetBulkRequest or InformRequest.
- Trap -Sent from the managed device to the NMS containing local system information.
- InformRequest -Sent as an acknowledgement to a Trap.
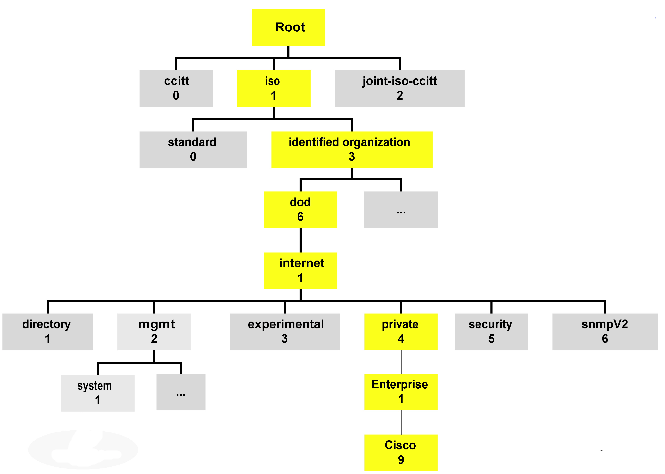
I like to think of the SNMP agent as an internal database that keeps track of the local managed device. This “SNMP database” is a structure composed of MIBs (Management Information Base), and each MIB contains a value that value is called an OID (Object Identifier). This structure is commonly referred to as a “tree” due to how it is represented, here is an example:
Each of those boxes represents a MIB and within those MIBs are groups of OIDs, each one containing information regarding the status of processes, interfaces, fans, power supplied, batteries, and many parts of the particular device. Something I really recommend (if you have not done it already) is walk the MIB tree of a few devices there are many free applications out there that perform MIB walks, just keep in mind there are some MIBs/OIDs that can be found on every devices but once you get past the standard MIBs every device different and memorizing MIB trees and OID values is near impossible but as long you understand the concept and know how to find what you need, you’ll be ok. Many vendors provide their MIB structure online on their website making finding particular OIDs very easy.
For further information you can see the following RFCs