Archive for March 2011
Cisco WLC Interfaces.
If you have ever worked with a Cisco WLC or have looked through any configurations for a WLC, then you have no doubt seen the interfaces that make it work. You’ve probably also seen that diagram concerning how these interfaces relate to the physical interfaces on a Cisco WLC.
Now their are only five different types of interfaces (Management, AP-Manager, Virtual, Service-Port, and Dynamic Interfaces), I figured I would just take some time to quickly touch on them.
- Management Interface – As you can suspect this interface is for in-band management and handles any communication with AAA servers. This interface will also handle the layer 2 communication between the controller and any APs. Needless to say the configuration of this interface is mandatory and can not be skipped.
- AP-Manager – If you want to have APs on different subnets other then the subnet the WLC is on then this interface must be configured, it’s a requirement for Layer 3 LWAPP transport mode. So as you would suspect this interface handles all layer 3 traffic between the WLC and the APs. Since higher end WLCs can have multiple AP-Managers only 1 AP-Manager interface can be configured per physical port.
- Virtual Interface – Another mandatory interface that must be configured (once again like the management interface you don’t get the option to skip the configuration of this interface). This interface handles any mobility management, VPN Termination, Web authentication, and is also a DHCP relay for WLAN clients. You really want to give this interface a bogus type address (Like 1.1.1.1 or something) since it’s only accessed and used by the WLC, the APs and WLAN clients will not interact with this interface. (Other then it’s purpose as the DHCP relay, but it’s all in done within the controller unknown to the AP’s or clients)
- Service-Port – This is also a physical port for out of band management, so it’s configuration is optional. The port doesn’t even support 802.1Q, so you can’t use it for anything other then accessing the controller. (Note: This is only physical port that is active while the controller is booting)
- Dynamic Interface – Now these are the interfaces you can create and use to link specific SSID’s to specific VLAN’s on the wire. So this is where and how you can separate your wireless client traffic, this interface will also double as the DHCP relay for it’s subnet/VLAN (Note: A WLC can have up to 512 dynamic interfaces)
How can you build a better network?
Often enough network engineers will be called upon to setup a network from the ground up. Whether it be a new branch office or a data center redesign it will be up to you to think up an efficient network design that can also be incorporated into the existing network seamlessly. Now depending on the size of the network that can be a daunting task, other times it could just be a simple ISR with an etherswitch module inside.
When you have to consider VLANs, Spanning-Tree, IP Addressing, Security, QoS, VoIP, Security, L3 redundancy, WAN connections, hardware models, software version, and the list goes on daunting at first yes? Cisco does have ample resources out there to aid you in your task of designing Cisco networks who would have thought?
One of the best resources I’ve found is the Cisco Design Zone this great website holds design details based on Technology, Industry, and architecture. While some of the guides can be quite large they go into very fine detail. The guides define advantages about using specific Cisco router or switch models along with sample configurations (best part in my opinion, seeing how it’s done) and some of the sample configurations have very convenient comments explaining the important points of the configurations. To sweeten the deal even more some of the guides show how the design correlates with Cisco’s SONA model which just adds volumes of worth while knowledge.
Addition resources can be found by looking at the Cisco design certification track the CCDA & CCDP programs have certification prep books from Cisco Press. They offer some great reference on best practice methodology concerning network design. The PPDIOO design model is also a good principle to abide by.
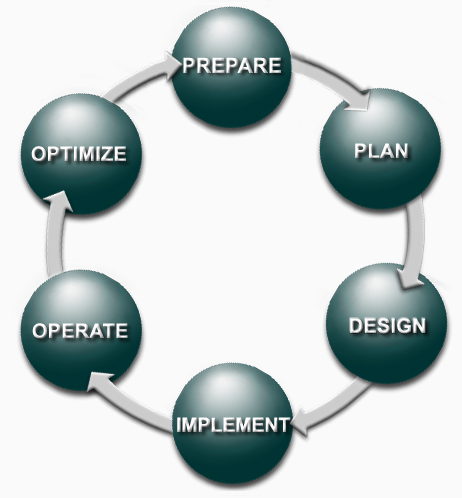 This PPDIOO design model is covered in great detail in the design track so if it’s something that interests you I would definitely pick up one of those books. (Just watch and make sure you get the book that correlates with the current exam version if you are planning to take the certification exam)
This PPDIOO design model is covered in great detail in the design track so if it’s something that interests you I would definitely pick up one of those books. (Just watch and make sure you get the book that correlates with the current exam version if you are planning to take the certification exam)
The last little piece I want to show is Cisco’s Campus Design model, it’s a nice extension of Cisco’s hierarchical model that’s shown in the CCNA track. (And once again, most if not all of the guides in the Design Zone will incorporate this model into the design)
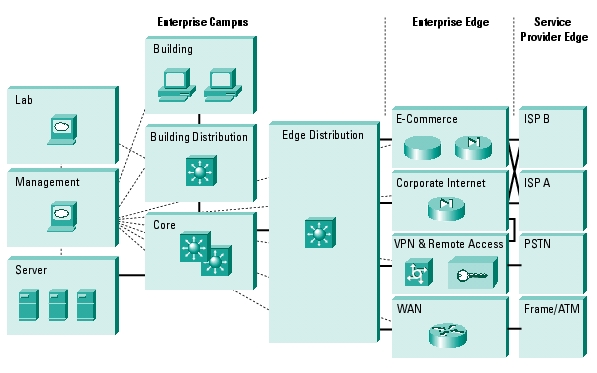 You can still see the Core, Distribution, and Access layers but you can also see the addition of many other layers a WAN layer for branch office connectivity, Internet layer, E-Commerce layer concerning where the rest of the world interacts with your companies public facing services, along with a few others. It breaks down any complicated network into a structured module portioning out where each device belongs.
You can still see the Core, Distribution, and Access layers but you can also see the addition of many other layers a WAN layer for branch office connectivity, Internet layer, E-Commerce layer concerning where the rest of the world interacts with your companies public facing services, along with a few others. It breaks down any complicated network into a structured module portioning out where each device belongs.
Now i’ve barely scratched the surface of Cisco’s network design concepts but if you want to see more definitely put the CDDA/CCDP books in your reading list, along with some guides from the Cisco Design Zone.
Secure Cisco Device Management.
One thing that should be standard in your setup, is secure management. Being a network engineer requires you to secure your management interfaces, whether the management interface is a web page or remote CLI session, it should be encrypted and authenticated. After all configuring port security and firewalls are useless if your administrative credentials are sniffed off the network in clear text, or worst case your entire configuration.
First thing you want to do is activate the secure protocols and disable the weak protocols. So we would issue the following commands:
As you can see we first disabled the HTTP protocol, and then enabled HTTPS (Note: the first time you enable HTTPS a certificate may be generated), then configured the vty lines to accept only SSH, and not telnet connections.
Note: Prior to disabling telnet and enabling SSH, you want to configure the aaa new-model parameters along with any local users DB entries. See this Cisco guide for configuring SSH in more detail. Last thing you want to do is lose remote access to your device.
Now this device can only be managed via HTTPS or SSH, telnet and HTTP access have been disabled. This will prevent the administrative credentials of your network devices from being sniffed off the network in clear text, only encrypted cipher text will be found.
Just to push the point home some more, here is a TCP stream where I telnetted into a lab switch and issued the sh run command. First off you see the password I entered to access the switch and secondly the entire output of the sh run command is right there in clear text!
Now, I did a second capture where I accessed the switch via SSH and issued the same commands.
Very different output, as you can see, in the beginning you see I used Putty after that the encryption algorithm exchange and the rest is cipher text.
You can also verify this by using NMAP to perform a port scan on the device to see what ports the device is listening on.
Here is a NMAP Scan with all four protocols enabled (Telnet, SSH, HTTP, and HTTPS)
Here you can see, the lab switch is listening on all four ports, so individuals can connect to this device in an insecure manner. (The option should not even be out there)
Now a second NMAP scan after the commands shown above were entered.
Now the device is only listening on 22 and 443. This device can only be managed in a secure way.
I’ll end this on a final note… The tools I used here are all free to download NMAP, WireShark, and Putty. So it doesn’t take much for some barely knowledgeable (and bored) user on your network to start sniffing packets on your network.
Let’s look at: Cisco Discovery Protocol (CDP)
Yes, yes I know if you have ever worked or studied Cisco on any level you will already be aware of Cisco Discovery Protocol (CDP), and what it is and does. I just wanted to take the time and cover it for some of it’s finer points. While I know talking about CDP is a jump from previous articles, but I was using Wireshark recently and caught a glimpse of a few CDP frames crossing my network.
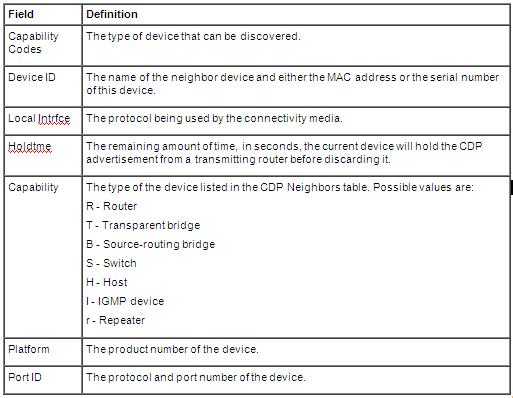
Now if you ever have to map out an all Cisco network then CDP in your road map, CDP will guide you to any neighboring Cisco devices providing you the below information:
Just look at that, the only thing it doesn’t give you is the amount the memory and flash in the neighboring device, so this also an easy way to inventory your network and see what devices are connected where and what IOS is running on that device.
To see this information from within a Cisco device you want to issue the sh cdp neighbors command
The output can easily be matched with the table posted above. Additionally you can issue the sh cdp neighbors detail command to go an addition step further and get the actual IOS version running the on the neighboring devices.
Along with the IOS version, addition details about the connected interfaces, and platform are displayed. So if you were in the process of mapping or auditing a network with only the tools available CDP is one that should never be overlooked.
Another thing to consider is which version of CDP is running on your Cisco devices, the screen shots above are both from devices running CDP versions 2. Obviously version 2 has a few additions that version 1 did not have, let’s compare the two shall we.
As you can see version 2 offers improvements with PoE negotiation, which is used with other Cisco devices (VoIP phones, and Cisco AP’s), as well as duplex settings, the native VLAN of the line, and the VTP management domain information.
The last thing I want to mention is the CDP packets I sniffed off my lab can be sniffed from any Cisco device if CDP is running on the interface, which can be security risk especially on edge devices. So on any edge devices or devices that do not have any other neighboring Cisco devices then you might as well disable CDP on the device, see my previous post concerning the 1-step router lockdown, concerning some basic security practices.