Archive for January 2012
Debugging a specific IPSec VPN.
Let’s say you’ve got a router with well over 100 IPSec VPN peers, and you’ve got this one tunnel that just won’t form correctly. Your not sure why and want nothing more than to debug the IPSec process for this one peer but you know if you debug the isakmp or ipsec process your going to suck up way too much resources, what do you do? Well we are going to debug the IPSec process, but we are going to debug this for only the specific peer we are having trouble with.
First thing we need to do is define our debug crypto condition.
As you can see we can debug by quite a few different criteria, many of which will come in handy (some more than others).
So let’s create a condition that will look for a specific peer address.
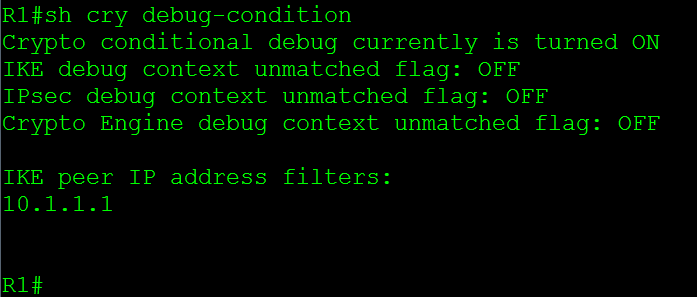
Now if (or I should say when) you want to check the current debug crypto conditions you can issue the sh crypto debug-condition command, this is a good way for you check and see whether or not someone left a condition in there from a previous troubleshooting session that could affect the output you’re looking for:
So the sh crypto debug-condition tells us the conditional debugging is turned on and it’s filtering by the IKE peer IP Address. Now when you start debugging the crypto process you will only see messages that match the peer address of 10.1.1.1, which will certainly make looking through debug logs much easier.
Now if we want to disable our existing crypto debug filters, we issue the debug crypto condition reset command, this will remove all existing conditions and allow us to add new filters to troubleshoot another issue.
Working with Cisco Access Control Lists / ACLs.
I know ACLs, how complicated can they be and how hard is it to work with ACLs? Not a very tough concept right, well what happens when you want to add ACEs (Access Control Entry) into an ACL before other entries? Remember an ACL will match from the top down. I’ve seen people completely rip out an ACL just to put it back in with one addition entry. Let’s take a look at an ACL and what we can do to change this around.
Now here we got a simple ACL:
First thing we see on the left is the sequence number for each specific ACE, remember all ACEs are given a sequence number, and by default the first ACE starts at sequence number 10, and any subsequent ACEs are given a sequence number 10 digits up. This is why the sequence numbers are incrementing by 10.
Now, let’s say the 192.168.2.0 /24 network was recently subnetted and we need to deny FTP traffic from the 192.168.2.0 /25 subnet, well we need to add the new entries before sequence number 20. So let’s jump into ACL Configuration mode and see what we can do.
So from global configuration mode we enter ip access-list extended OutBoundAccess, make note you can also change standard ACLs like this. So this is not just limited to extended ACLs. Notice the configuration mode has changed, now we are in R1(config-ext-nacl)# allowing us to continue configuring this OutBoundAccess ACL. So let’s go ahead and continue with our configuration, first we want to start with a sequence number lower then 20 and we want to deny FTP traffic from the 192.168.2.0 /25 subnet.
Once we add the command we can issue the show command to verify the new ACE is in the correct location, and indeed it is.
Now let’s go a step further, let’s say we ran out of sequence numbers between 10 to 20 and we need get a few more ACEs in there.
Sure, we could add them before sequence number 10 but for the sake of this example let’s see we can’t. What we need to do is re-sequence the ACL.
We entered the command ip access-list resequence OutBoundAccess 10 10 resequencing the OutBoundACL starting with sequence number 10, in increments of 10. Look at the sequence numbers now. This allows us to keep adding entries where we need to. This definitely makes it easier to add entries and move entries around an ACL with minimal effort.
Passed QoS and got my CCIP!
Well after 7 months of studying and 2 exams later I’ve finally obtained my CCIP! When I initially thought about going after my CCIP I said this shouldn’t be too bad after going through Routing TCP/IP Volume II, BGP Design & implementation, and half way through MPLS fundamentals (See my Library page on the left for links) I was really starting to feel it. I kept moving along and passed the 642-691 I got a little bit of hope and jumped right into QoS. The funny thing about QoS was I didn’t realize how much I really new about it, nor did realize how much more I could do with it. QoS certainly was an interesting topic to learn, and I am sure I’ll be learning even more about it as time goes on.
Now that I’m done with my CCIP, I think I am going to take a small break from studying. I am going to focus back on my blog (So hopefully I will get some more updates out) and I am going to start building my own home lab for whenever I decide to start studying for my CCIE (not sure when but I will pursue that eventually). Not a bad way to start the new year right?
Welcome 2012!!
Hello 2012! I know I’m day late here but having finally gotten over a pretty nasty cold I can finally start the new year! A toast and a look back at 2011 to all the successes and failures it brought us, to all the lessons we learned, to all the friends we made, and people we met. May 2012 make us even greater and smarter than 2011 did!
2011 saw me starting a new position as network engineer for managed services provider, and getting my Server+, CCDA, CWTS, and passing my BGP+MPLS exam. I didn’t quite get to finish my CCIP in 2011 but I’ve got plenty of time in 2012 to take the QoS exam. I’ve got plans for 2012 (CCIP, CCDP, maybe start CCIE), and if your reading my blog I’m sure you got plans as well.
Here’s to you, me, and our goals may we both work hard to reach those goals!