Archive for the ‘IPS’ Category
End-Of-Sale date announced for various Cisco IPS’s
Since Cisco started announcing the Sourcefire FirePower (Hardware & Software) modules earlier this year I have been wondering what was going to happen to their existing IPS line. Looks like the End Of Sale announcement was recently made, with an EoS date in April of next year.
The EoX announce affects both the IPS Modules and IPS 4xxx sensor platforms. IOS IPS will remain available, but I do wonder for how long?
This will be an interesting shift for those of us that have used the original Cisco IPS software for a long time now. As we know there is more that goes into this than just buying a module or IPS Appliance. we will also need a central management server to quickly and easily manage these types of devices. Monitoring signature updates and keeping singatures in-sync company wide can be a massive problem if you don’t have it under your thumb. So far I have not seen any support added for SourceFire in Cisco Security Manager, so FireSIGHT will be the way to go.
I wonder if anything will happen to the CX Modules, since they ran their own Next-Generation IPS Signature set. Time will tell I suppose.
When does the Cisco ASA IPS module inspect traffic?
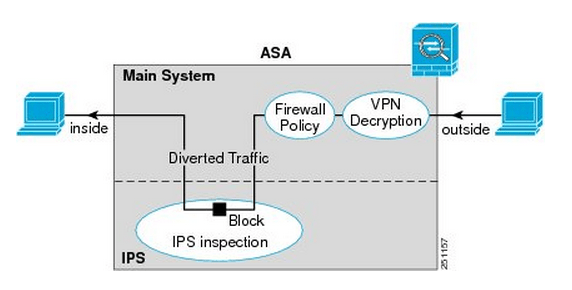
Sure we can put an IPS module inside an Cisco ASA firewall but the first you may ask or will be asked is at what point does that traffic get inspected by the IPS Module? Which might not seem like a tough question but it can make you think if you got VPNs terminating on your ASA, does it inspect the traffic before encryption, after encryption, or is encrypted traffic bypassed? I did a post about the packet flow through a Cisco ASA some time ago and it did mention the IPS is involved after NATs, application inspection, and even ACLs however there was no mention of how encrypted VPN traffic.
Well, as it turns out the traffic is redirected to the IPS module after it enters the ASA on the ingress interface, the VPN traffic is decrypted, and the firewall inspection policies have been applied. Now for outgoing VPN traffic the IPS inspects that traffic and then it is encrypted and sent through the IPSec connection. Makes perfect sense.
Here is a quick visual from Cisco.com:
You’ll notice once the traffic enters from the outside interface, if it is VPN traffic it is then decrypted sent though the firewall policies and is then diverted to the IPS module. Once the IPS module has had a chance to inspect the traffic it is then sent back to the ASA to be sent out the inside interface.
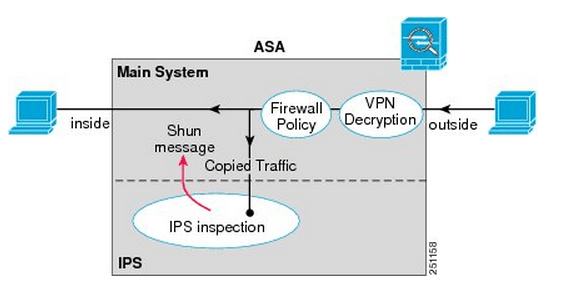
Something I want to point out the IPS Modules work in 2 different modes, inline mode which is shown above where the traffic is sent through the IPS module and back into the ASA this mode may degrade throughput depending on the model of the module and the amount of traffic being inspected. We also have Promiscuous mode where the traffic is not sent directly though the IPS Module but the IPS module instead receives a copy of the traffic to inspect. The upside of promiscuous mode is the fact throughput is not effected however it is less secure than inline mode since the traffic sent to its destination at the same time it sent to the IPS module, the IPS module however can sent a RST packet ending connection or ‘shun’ the offensive IP address. When an address is ‘shunned’ any traffic from that source is dropped.
Here is a quick visual of promiscuous mode:
You can read more about the IPS ASA module inspection process here.