Debugging a specific IPSec VPN.
Let’s say you’ve got a router with well over 100 IPSec VPN peers, and you’ve got this one tunnel that just won’t form correctly. Your not sure why and want nothing more than to debug the IPSec process for this one peer but you know if you debug the isakmp or ipsec process your going to suck up way too much resources, what do you do? Well we are going to debug the IPSec process, but we are going to debug this for only the specific peer we are having trouble with.
First thing we need to do is define our debug crypto condition.
As you can see we can debug by quite a few different criteria, many of which will come in handy (some more than others).
So let’s create a condition that will look for a specific peer address.
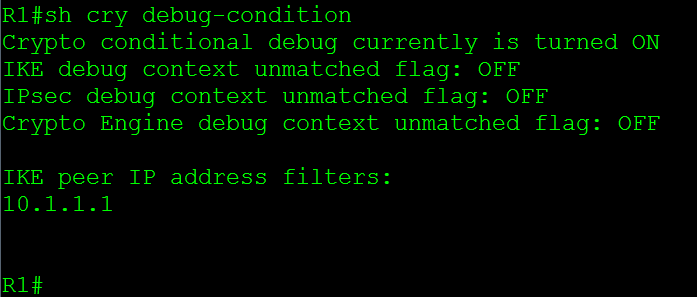
Now if (or I should say when) you want to check the current debug crypto conditions you can issue the sh crypto debug-condition command, this is a good way for you check and see whether or not someone left a condition in there from a previous troubleshooting session that could affect the output you’re looking for:
So the sh crypto debug-condition tells us the conditional debugging is turned on and it’s filtering by the IKE peer IP Address. Now when you start debugging the crypto process you will only see messages that match the peer address of 10.1.1.1, which will certainly make looking through debug logs much easier.
Now if we want to disable our existing crypto debug filters, we issue the debug crypto condition reset command, this will remove all existing conditions and allow us to add new filters to troubleshoot another issue.




Leave a comment