Wireshark Tid-bit: De-crypt SNMPv3 in Wireshark
I recently found myself troubleshooting some SNMP connectivity between a particular set of devices and an NMS. Connectivity did not appear to be the problem as IP Connectivity was there and MIB walks were successful, however some interesting errors were still getting reported on the NMS. As I captured the packets to verify this connectivity, I said to myself ‘If only I can see what the NMS was asking for specifically and what device in question was replying back with’. This led me to check out the SNMP protocol settings in Wireshark, I mean Wireshark can de-crypt HTTPS traffic (with the private key) and wireless WPA traffic surely it can de-crypt SNMPv3. Behold it was true!! I was able to de-crypt SNMPv3 packets, and see what was really going on.
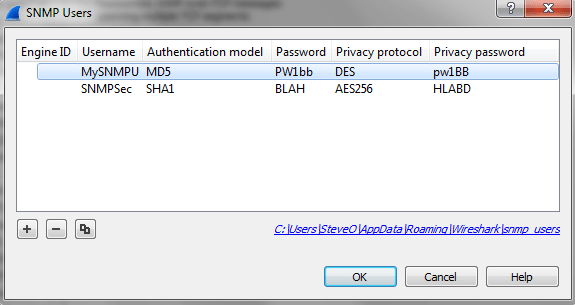
To add SNMPv3 information into Wireshark:
Access your Wireshark preferences: Edit -> Preferences -> Protocols -> SNMP
Where you see ‘Users table’ choose edit:
From here we can enter the SNMPv3 settings we need:
- Engine ID
- SNMP USer
- Authentication & Password – MD5 or SHA1
- Privacy & Password- DES, AES-128, AES-192, or AES-256
Once you enter the correct information and choose ‘ok‘ Wireshark will automatically de-crypt any relevant packets.
I feel like this is something I should have known about for a while now, but I supposed I don’t find myself troubleshooting SNMP connectivity too often. Figured I would get the word out there!


Good one
Roshan
May 8, 2016 at 1:20 PM