Configuring TCP intercept.
SYN floods are a pretty common DoS attack that can be performed on any TCP based (FTP, Web Server, Email, etc) application over the internet, luckily our normal run the mill Cisco IOS ISR routers have a feature known as TCP Intercept that can protect your servers from this type of attack.
TCP Intercept operates in 2 different modes but the overall concept is the same, TCP intercept will take into account every SYN packet from the client that traverses the router and if the connection remains half-open or there are so many half-open connections the router will start sent sending rest (RST) packets to close that connection. Half-open connection are those that do not fully complete the TCP handshake (SYN, SYN-ACK, ACK process).
The first of two modes that TCP Intercept operates in is intercept mode. In this mode the router actually accepts the SYN and responds to the source with the SYN-ACK packet, if the client completes the connection by sending the ACK the router then passes the original SYN to the destination and negotiates the connection with server, the client is completely unaware this process is even going on. The only thing to keep in mind with the intercept feature is that the router only keeps track of the TCP packet type, it does not take into account any TCP options within the packet (ie: window scaling or other TCP features within RFC 1323).
Here is a diagram of the process (This image is from Cisco Press: Cisco Router Firewall Security’s book)
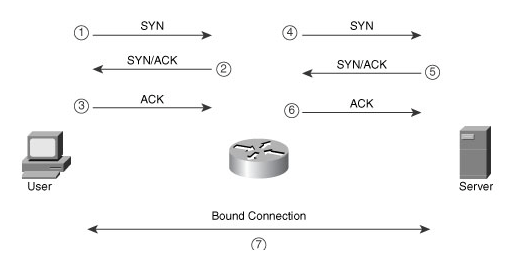
TCP Intercept in Intercept mode capturing every SYN packet and acting as buffer protecting the server behind.
TCP Intercept can also operate in a watch mode in this mode the router takes a much more passive approach. In this mode the router does respond to any SYN packet it just sits back and watches the TCP handshake process. If the router notices a connection is half-open for so many seconds it will send a RST packet to the server so the server closes the half-open connection.
Now that we have an understanding of TCP Intercept let’s go ahead and configure TCP intercept.
TCP intercept is configured from global config mode and we have quite a few configurations options here. I’m going to configure TCP Intercept for both watch and intercept mode and we will go through the configurations:
This watch mode configuration accomplishes the following:
- Sets the TCP Intercept mode to watch mode. ip tcp intercept mode watch
- TCP Intercept is configured to monitored TCP connection to servers matched in the TCPInterceptACL access-list, this provides us granular control of the servers and ports we want to monitor. ip tcp intercept list TCPInterceptACL
- The router will transmit a RST packet to servers if the connection is not established within 8 seconds. ip tcp intercept watch-timeout 8
- TCP Intercept will enter an aggressive mode and start dropping the oldest TCP connection if there are 500 half-open TCP connections until that number is below 400 half-open TCP connection. ip tcp intercept max-incomplete high 500 & ip tcp intercept max-incomplete low 400
- TCP Intercept will enter an aggressive mode and start dropping the oldest TCP connection if 300 connection requests within one minute until that number is below 200 requests a minute. ip tcp intercept one-minute high 300 & ip tcp intercept one-minute low 200
- TCP Intercept will close and any connection that has been open for 8 hours (28800 seconds) with no activity. ip tcp intercept connection-timeout 28800
The above TCP Intercept intercept mode configuration is very similar to the previous watch mode but the first thing you will notice is the fact it doesn’t tell you it is operating in intercept mode, this is because it operates in intercept mode by default. You also notice 2 additional commands in here:
- ip tcp intercept finrst-timeout 20 this tells to router when it sees a TCP connection being torn down, if that connection is not closed within 20 seconds the router will close the connection itself by sending a RST packet.
- ip tcp intercept drop-mode random when TCP Intercept starts aggressively dropping connections by default it drops the oldest connections, this behavior can be changed so the router drops random TCP connections instead of the oldest connections.
You can verify how TCP Intercept is interacting with your traffic by issuing the following commands:
- show ip tcp intercept statistics – This will give you a quick look at incomplete, established, & how many connection requests have been made to the servers matched by the ACL.
- show ip tcp intercept connections – This command shows you all the current connections TCP Intercept is working with/watching.
- You can also use debug ip tcp intercept to quickly see what TCP Intercept is doing in real-time.
Now if you want to fully lab this feature out and see it in action you can set up a client/server enviroment in your lab and either configure an ACL to block ACKs from your source client or use a program call Scapy to transmit SYN packets.
Sample ACL:
access-list 101 deny tcp host hostaddress eq portnumber host destination ack
Sample Scapy SYN packet:
sr1(IP(dst=”destinationIP“)/TCP(dport=destinationPortNumber,flags=”S”))




I believe your show commands are incorrect. On my IOS XE 16.x and IOS 12.4 it is just:
show tcp intercept statistics
show tcp intercept connections
The debug command line is correct though.
Paul Cahill
October 2, 2018 at 1:26 PM