Configuring DMVPN.
Since I covered the basics of NHRP, now seems like the best time to tackle the configuration of DMVPN on Cisco IOS routers. I’m going simply build off of my last NHRP post, so we are going to have a single hub router and 2 spoke sites, we are going to adding encryption to our DMVPN using tunnel protection.
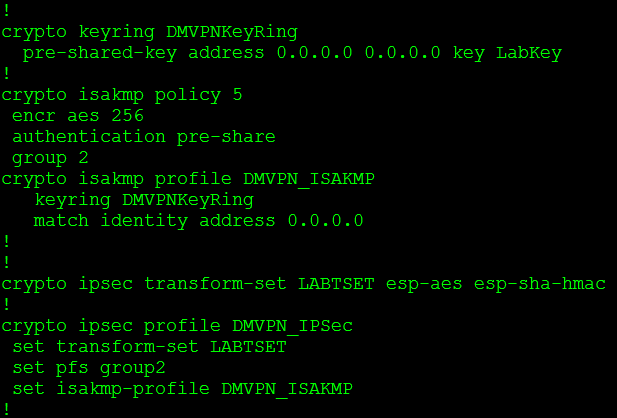
So lets first configure our IPSec parameters:
For a more in depth look at these commands refer to my older post Encrypted GRE tunnels.
Now that we have the IPSec parameters configured let’s go ahead and configure our tunnel interface for an encrypted DMVPN, so let’s start with the hub:
So there it is, the DMVPN hub, only a few these commands are typical of a normal GRE tunnel but most of them are specific to the DMVPN configuration. Let’s talk about a few these commands:
- ip nhrp authentication password: This command allows you to specify a password for your DMVPN network so not just any GRE tunnel can join your DMVPN cloud. (This is just one a few different mechanism to control who can participate within your DMVPN network)
- ip nhrp map multicast dynamic: This command allows NHRP to automatically map multicast traffic from other devices, without the need to statically configure each device. So this command is how our NHS builds its “nhrp database”
- ip nhrp network-id number: The NHRP network-id number ensures this DMVPN interface only participates within it’s own DMVPN network. Just in case you have more the one tunnel interface on the same router connected to two separate DMVPN clouds/networks.
- tunnel mode gre multipoint: This specifies the tunnel interface an GRE multipoint meaning this will be acting as single interfaces connected to multiple peers
- tunnel key number: This is another mechanism to keep your DMVPN network clean of any unwanted members, this is actually built into the GRE encapsulation itself, only GRE’s tunnels with the same tunnel key can communicate. So if the hub is using Tunnel key 10, then the spoke must use tunnel key 10 as well, if not then they will not be able to communicate.
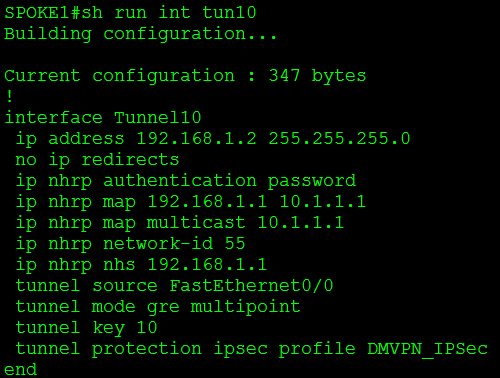
Now let’s look at the spoke:
Now most of these commands are identical to that found on the hub, with the exception of the following:
- ip nhrp nhs 192.168.1.1: This commands specifies the Next Hop Server for the spoke
- ip nhrp map 192.168.1.1 10.1.1.1: This command maps the NHS GRE (protocol) address to it’s physical interface (NBMA) address.
- ip nhrp map multicast 10.1.1.1: This tells the NHC where to send its multicast traffic to.
And to reinforce that here is the configuration from the second spoke in this DMVPN network:
Identical to the first spoke (with the exception of the ip address).
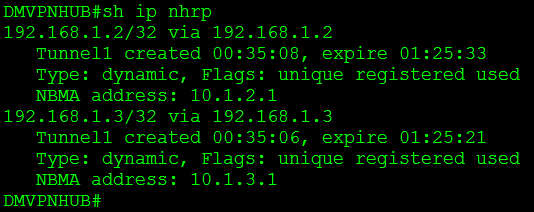
So now that we have this configuration how do we verify our DMVPN is working, well let’s check our NHRP mappings along with our routing.
We issue the command sh ip nhrp this tells us we have NHRP mappings to both spokes 192.168.1.2 and 192.168.1.3.
Now let’s check the routing, I’ve configured these 3 routers to speak via eBGP:
So from this you’ll notice our hub has 2 eBGP adjacencies with our spokes, and we are are learning a few prefixes from those spokes.
But, now for the ultimate test, lets get spoke1 and spoke2 to create a direct tunnel between themselves.
From the top to bottom, you’ll notice Spoke2 only has NHRP mapping to the hub. I perform a traceroute to spoke1 and you see it bounce off the hub and then hit spoke1 I then perform the same traceroute a second later and it directly hits spoke1 bypassing the hub completely. Now when I issue the sh ip nhrp command you notice I still have my NHRP mapping to the hub at 192.168.1.1, but I also have a new NHRP mapping to spoke1 at 192.168.1.2. So our DMVPN is working successfully!
While this is a small victory, the topic of DMVPN is a fairly large one and we still have a few more topics to cover:
- How DMVPN interacts with IGPs. (Think about this one, some of the tools we rely on to prevent routing loops will be working against here)
- Different “phases” of DMVPN networks.
- Dual cloud DMVPN networks.
So stay tuned there is more to come!





Leave a comment