Verifying IPSec tunnels.
I know my last few posts have been focused on either how IPSec functions or the configuration so now that we know how to configure IPSec how can we make sure our IPSec VPN is up, functional, and passing traffic? Well there are a few different commands we can issue to check on the status or our IPSec VPN:
Show crypto isakmp sa
This command will tell us the status of our negotiations, here are some of the common ISAKMP SA status’
The following four modes are found in IKE main mode
- MM_NO_STATE* – ISAKMP SA process has started but has not continued to form (typically due to a connectivity issue with the peer)
- MM_SA_SETUP* – Both peers agree on ISAKMP SA parameters and will move along the process
- MM_KEY_EXCH* – Both peers exchange their DH keys and are generating their secret keys. (This state could also mean there is a mis-matched authentication type or PSK, if it does not proceed to the next step)
- MM_KEY_AUTH* – ISAKMP SA’s have been authenticated in main mode and will proceed to QM_IDLE immediately.
The following three modes are found in IKE aggressive mode
- AG_NO_STATE** – ISAKMP SA process has started but has not continued to form (typically do to a connectivity issue with the peer)
- AG_INIT_EXCH** – Peers have exchanged their first set of packets in aggressive mode, but have not authenticated yet.
- AG_AUTH** – ISAKMP SA’s have been authenticated in aggressive mode and will proceed to QM_IDLE immediately.
The following mode is found in IKE Quick Mode, phase 2
- QM_IDLE*** – The ISAKMP SA is idle and authenticated
- sh crypto ipsec sa – Now this output can really daunting at first just due to the amount of information that is displayed here but there are a few key things to watch out for. Such as the #pkts encaps/encrypt/decap/decrypt, these numbers tell us how many packets have actually traversed the IPSec tunnel and also verifies we are receiving traffic back from the remote end of the VPN tunnel. This will also tell us the local and remote SPI, transform-set, DH group, & the tunnel mode for IPSec SA.
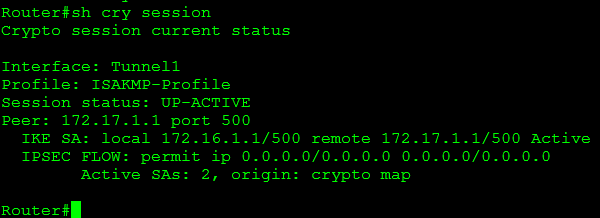
- sh crypto session – This command will give you a quick list of all IKE and IPSec SA sessions.
Some of the common session statuses are as follows:
- Up-Active – IPSec SA is up/active and transferring data.
- Up-IDLE – IPSsc SA is up, but there is not data going over the tunnel
- Up-No-IKE – This occurs when one end of the VPN tunnel terminates the IPSec VPN and the remote end attempts to keep using the original SPI, this can be avoided by issuing crypto isakmp invalid-spi-recovery
- Down-Negotiating – The tunnel is down but still negotiating parameters to complete the tunnel.
- Down – The VPN tunnel is down.
So using the commands mentioned above you can easily verify whether or not an IPSec tunnel is active, down, or still negotiating. Next up we will look at debugging and troubleshooting IPSec VPNs
* – Found in IKE phase I main mode
** – Found in IKE phase I aggressive mode
*** – Found in IKE phase II quick mode



hi
while delivering show crypto session command, one site showing up_active( branch) and the peer showing down_ negotiating (head ofice )… what is the reason???
Arun
July 6, 2013 at 3:40 AM
[…] Verifying IPSec Tunnels […]
It’s been 5 years!! | CCIE or Null!
September 14, 2015 at 9:01 AM