IPSec on a Cisco IOS router.
In my previous post I covered some basics on IKE and the process on which IPSec VPN’s form and negotiate their secure connection. So now I figured I’d continue that trend and cover the configuration of an IPSec VPN between 2 Cisco IOS routers.
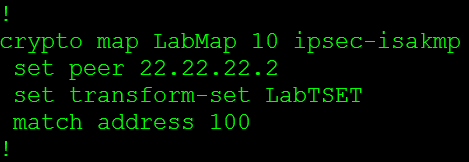
So let’s check out a large portion of the configuration right here:
This configuration snippet (the first 3 lines) includes the ISAKMP policy used in phase 1 negotiations, which specifies the encryption, hash, & authentication method. I also want to mention you can have multiple ISAKMP polices on the same router, the thing to remember is the ISAKMP policies will be negoatiated from the top down. So the first ISAKMP policy that matches the peer’s ISAKMP profile with the lowest sequence number is the policy that will be used. Which means it is best practice to place the more secure ISAKMP policies at the beginning of your policy, to ensure they get used over a weaker policy.
Right after the ISAKMP policy we have our PSK used to authenticate the specific peer. You can specify the address 0.0.0.0 0.0.0.0 to use the same key for all IPSec negotiations. So you would not need to specify a PSK for every particular peer.
Next we have our transform-set which provides us with our encryption options for phase 2 negotiations. Within the transform-set is were we can specify the encapsulation mode (tunnel or transport). Similar to the ISAKMP policy we can configure multiple transform-sets with completely different parameters in each one.
Now the Crypto Map is where we tie in a lot of these parameters and start linking it to the peer. The first thing we set is the peer’s address, and then we will specify the transform-set that will be used with this particular connection. I want to mention we can configure multiple transform-sets for a single peer and during the negotiations a matching transform-set will be used. The last thing in this crypto-map is the match address 100 this is where we specify what traffic gets encrypted, this is known as interesting traffic. This matches to an ACL.
So all traffic that goes between the 192.168.1.0/24 and the 192.168.2.0/24 network will get encrypted.
Now the last thing we need to do is apply that crypto map to physical interface.
Now we can only have a single crypto map applied to a physical interface, so the next question is how do we configure multiple VPNs to terminate to a single router? Well we configure multiple entries using the same crypto map, we do this by using a different sequence number for each peer.
So from the above screen shot the sequence number after the crypto map is different, these sequence numbers can go from 1 – 65355 so you have more then enough sequence numbers to terminate multiple IPSec VPNs to a router. Of course you will never want to terminate 65355’s VPNs to a single due to performance.
The next thing I want to mention is how to configure a single crypto map to form VPNs using main mode or aggressive mode. This might sounds tricky at first since you can only have a single crypto map assigned to a single interface but it’s really pretty simple, all you have to do is use the same name you used for the existing crypto map.
So to recap the pieces we need to create a policy based IPSec VPN
- The ISAKMP Policy
- The Transforms-Set
- The Pre-shared key
- The Crypto Map
- Access-list








Leave a comment